Support Tip: Different techniques and a comparison of enrolling a Windows 10 device to Intune and an overview of the logs
My name is Saurabh Sarkar and I am an Intune engineer in Microsoft. I have a YouTube channel ‘EverythingAboutIntune’ and you can subscribe to the same to learn more about Microsoft Intune.
The entire demonstration of this post which illustrates the different techniques of enrolling a Windows device can be found below-
Background:
In order to manage devices via Intune, devices must first be enrolled in the Intune service. Both personally owned and corporate-owned devices can be enrolled to Intune for management.
There are predominantly 2 methods of enrolling a device via Intune-
Manual and Automatic
- Manual enrollment involves the user to initiate the enrollment process.
- Automatic enrollment uses some mechanism to fetch the user’s/device’s credential and the user does not need to enter his cred again to initiate the enrollment.
- Manual enrollment is usually used in personal devices, while the Automatic enrollment is used for bulk enrollment of corporate devices to the enterprise
In this blog, we are going to get a brief overview of the various enrollment techniques of a Windows 10 device to Intune, do a comparison between all of them, and take a brief look over the relevant logs/registry locations.
Comparison:
- Let’s do a quick comparison between all the above discussed methods (based on intended devices and user experience):
| Enrollment Method | Device Ownership | User Interaction |
| Manual | Personal | Yes |
| Auto-Enroll | Personal | Yes |
| GPO | Corporate | No |
| AutoPilot | Corporate | Yes |
| Co-Management | Corporate | No |
| Deep Link | Personal | Yes |
| Company Portal App/Website | Personal | Yes |
| Windows Configuration Designer | Corporate | No |
Methods of Enrollment of a Windows 10 device to Intune
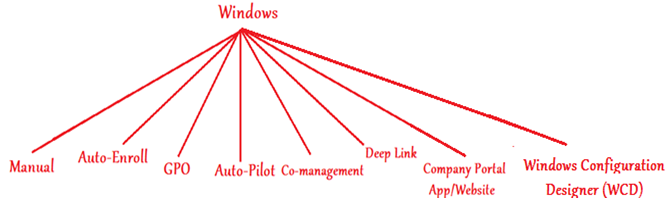
As shown above, there are 8 ways of enrolling a Windows device to Intune. Now let’s understand and get an overview of all the above methodologies.
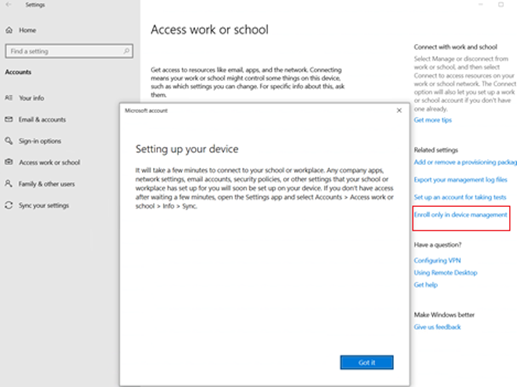
- Manual Enrollment: (‘Enroll only in devicemanagement’)
- If we wish to Enroll a device to Intune but not have any AAD Registration record of the device in Azure then we can have the user do a ‘Enroll only in device management’
- In this case the device is only enrolled to Intune but is not AAD Registered/Joined and we will not be seeing any record of this device in Azure once the process completes.
- Meaning- In this case the device shows up in “All Devices” tab in the portal but not under “Azure AD Devices”
- Doing this manual enrollment enables us to manage the device from Intune (MDM policies are applicable)
- This is usually done when the users don’t have an Azure AD license
- This enrolls the device as Personal
- This method isn’t recommended because it doesn’t register the device into Azure Active Directory.
- It prevents the use of features related to Azure such as Conditional Access.
- Path – Start>Settings>Accounts>Access Work or School> ‘Enroll only in device management’ hyperlink
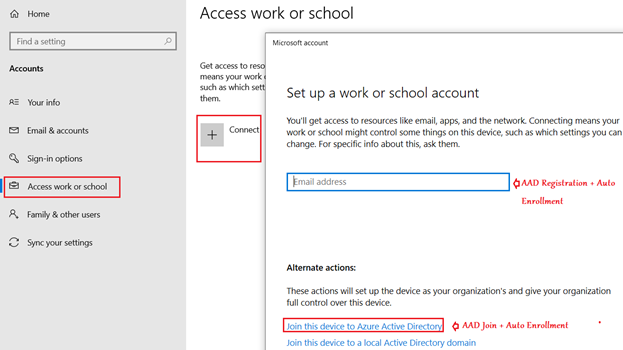
2- AutoEnroll:
- In this case the device is first AAD registered/Joined and once that happens, the device gets automatically enrolled to Intune.
- As the user only triggers the device join/registration to Azure but the device gets enrolled to Intune automatically, hence the term ‘Auto Enroll’
- The user needs to have an AAD Premium license to make use of this feature
- In this case the device shows up under both tab in portal- “All Devices” and “Azure AD Devices”
- The device shows us as Personal (In case of AAD registration + Enrollment) and Corporate (In case of AAD Join + Enrollment)
- The MDM scope in Azure AD needs to be set for this to work.
- For AAD Join + Intune auto enrollment scenario-
- The device should not be Windows 10 Home
- The device should not be joined to the on-prem domain
- The device should not be already MDM managed
- The logged in user needs to be an Admin.
- Path (AAD Registration + Auto Enrollment) Start>Settings>Accounts>Access Work or School>’Connect’
- Path (AAD Join + Auto Enrollment) à Start>Settings>Accounts>Access Work or School>Join this device to Azure Active Directory Hyperlink
The following blog explains how to setup the MDM Scope in Azure AD-
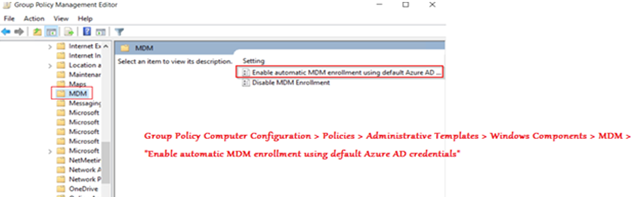
3- Group Policy Enrollment:
- As the above enrollment techniques were manual, it is not very much feasible to enroll thousands of machines an enterprise might potentially have as it has dependence on the end user’s action.
- Using Group policy, we can automate the device’s enrollment to Intune
- This approach is usually used for bulk enrollment of corporate on-prem domain joined devices
- The device must be Hybrid AAD Joined for this to work
- The AD-joined PC running Windows 10, version 1709 or later
- There should be an Azure AD PRT issued already
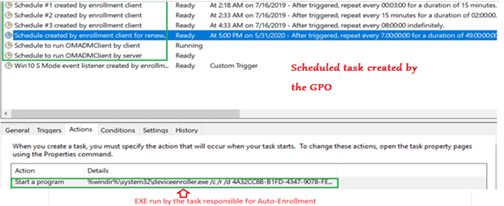
- In this technique we target the devices we wish to enroll via a GPO which creates a scheduled task that triggers the enrollment.
- In this case the device is enrolled as Corporate
For more details, please refer to-
Group Policy Editor:
Task Scheduler:
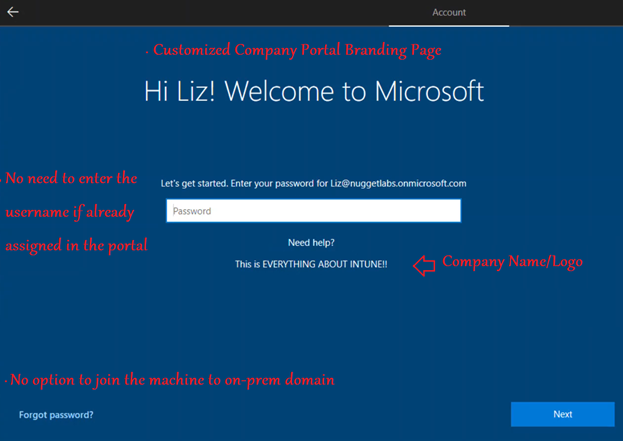
4- Autopilot
Using this approach, we do an AAD Join + Intune enrollment of a device during the oobe phase itself
- This solution is used for bulk fresh deployment of Windows devices.
- The devices are enrolled as Corporate
- We need to have the hardware hash/serial no. of the device to achieve this
- The device should be powered on for the first time/has to be rest
- MDM scope needs to be set for Autopilot
Please refer to the below doc for more details-
https://docs.microsoft.com/en-us/mem/intune/enrollment/enrollment-autopilot
Note-
- We can also do a Hybrid Azure AD Join Autopilot, in which the device is Hybrid Azure AD Joined and enrolled to Intune.
Kindly refer to the below for more details on the same-
https://docs.microsoft.com/en-us/mem/intune/enrollment/windows-autopilot-hybrid
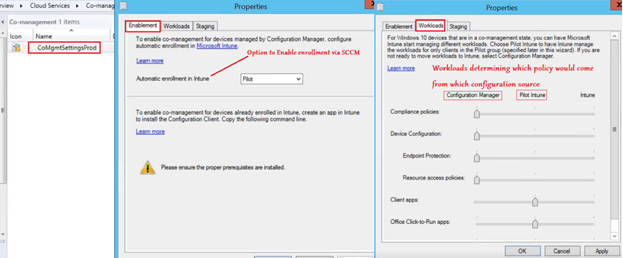
5- Co-management-
- This is another way of doing bulk enrollment of corporate, domain joined devices.
If the devices already have a SCCM client and are managed by configmgr then the same can be leveraged to initiate enrollment of the device to Intune automatically.
- The device needs to be Hybrid Azure AD Joined
- Device needs to be Windows 10, version 1709 or later.
- The AzureADPrt needs to be present.
- Configuration Manager version 1710 or later.
- The device needs to be added to the relevant collection in the SCCM console for the Auto enrollment to happen.
- As the device is managed via Intune and SCCM simultaneously, we define workloads in the SCCM console which defines which policy would come from which configuration source
- The devices are enrolled as Corporate
- The Group Policy for enrollment is no longer needed in this case
Please refer to the below doc which explains the flow behind Auto-Enrollment via SCCM-
6- DeepLink
- Windows 10-based devices may be connected to work using a deep link.
- Users can select or open a link in a particular format from anywhere in Windows 10, and be directed to this enrollment experience.
- Device needs to be Windows 10, version 1607 or later
- IT admins can also add this link to an internal web page that users refer to enrollment instructions.
- This process is equivalent to doing a “Enroll only in device Management” from the UI
- The devices are enrolled as Personal
- URI to be used – ms-device-enrollment:?mode=mdm
#1-
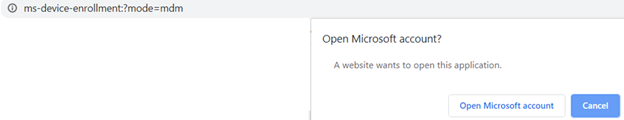
#2-
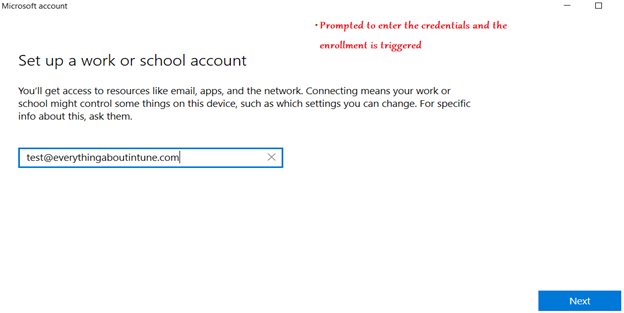
7- Company Portal App/Website:
- Open Microsoft Store >In the Search field, type Company Portal>In the list of results, select Company Portal > Install.
- Installing the Company portal app is not mandatory for enrolling a Windows 10 device to Intune.
- The advantage of installing the Company portal app is- it gives us the ability to view and install Available (optional) applications which has been provisioned by the organization’s admin.
Company Portal App:
- The app is available in Microsoft Store
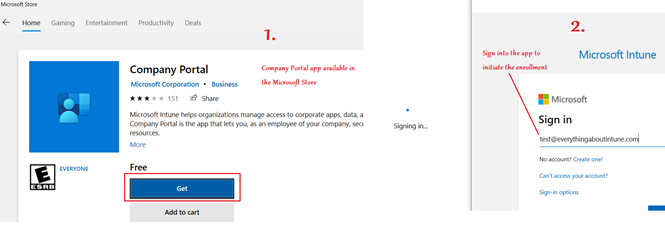
Company Portal Website:
- The website for the same is- portal.manage.microsoft.com
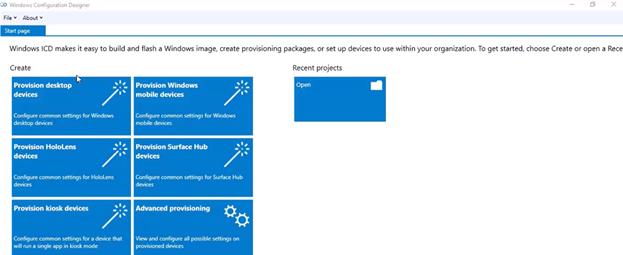
8- Windows Configuration Designer:
- Using Windows provisioning, administrators can seamlessly set up the configurations and settings and deploy the same to bulk devices.
- A provision package can be used to add devices in bulk to Azure AD and automatically enroll those devices into Microsoft Intune.
- A provisioning package file (.ppkg) is a container for a collection of configuration settings.
The provisioning package can be created by using the Windows Configuration Designer.
- The package can be installed via USB media during initial Windows OOBE experience or from existing Windows PC desktop screen.
- There is an overhead of copying the .ppkg to all the machines via a removable media
- This is used for bulk enrollment of Corporate-owned devices
- This method does not allow the use of Conditional Access.
For more details on this, kindly refer to the below link-
https://docs.microsoft.com/en-us/mem/intune/enrollment/windows-bulk-enroll
Logs:
Once a Windows device has been successfully enrolled, we can check the flow in the below location-
- Eventviewer à Userdevice Registration | Device Management-Enterprise Provider
- MDM Diagonistic Logs
- Registry location
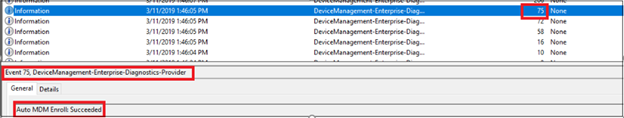
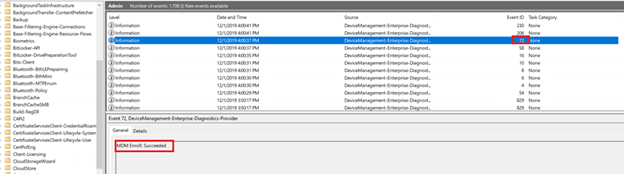
Eventviewer:
- Below is the flow we can observe in the Eventlogs:
| Event Message | Successful Event ID |
| Certificate policy request sent successfully | 4 |
| Certificate policy response processed successfully | 6 |
| Certificate enrollment request sent successfully | 8 |
| Certificate enrollment response parsed successfully | 10 |
| OMA-DM client configuration succeeds | 16 |
| MDM Enroll: OMA-DM client configuration succeeds | 16 |
| MDM Enroll: Succeeded | 72 |
| Auto MDM Enroll Succeeded || (SCCM/GPO) | 75 |
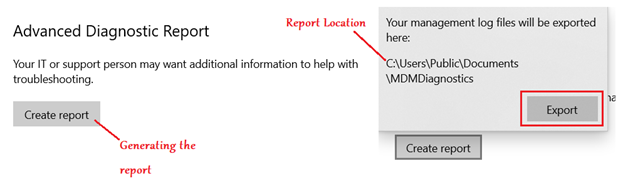
MDM Diag Logs:
- Location — Start>Settings>Accounts>Access Work or School>Info>Create Report
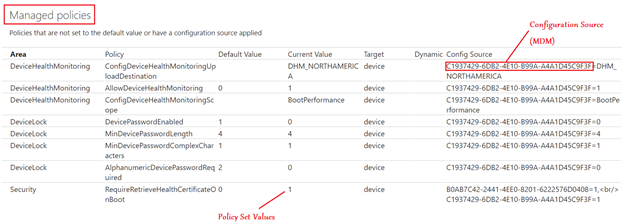
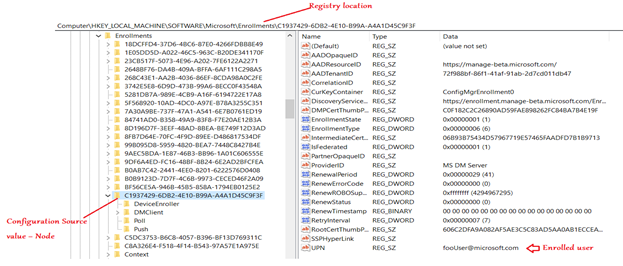
Registry:
- Registry location- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Enrollments\C1937429-6DB2-4E10-B99A-A4A1D45C9F3F (Config Source value key node)
Conclusion:
There are several ways of enrolling a Windows device to Intune. Choosing the right one would depend on our use case and other factors like the kind of devices in use(Personal/Corporate), the infrastructure present at our disposal(SCCM/Group policy-on-prem domain/Hardwarehash) and the scalability (personal/bulk)
Reference Links-
https://docs.microsoft.com/en-us/mem/intune/enrollment/enrollment-method-capab
https://docs.microsoft.com/en-us/windows/client-management/mdm/mdm-enrollment-of-windows-devices

Comments
Nice to have all the enrollment methods in one place. Good job.
Hmm it seems like your website ate my first comment (it was extremely long) so I guess I’ll just sum it up what I had written and say, I’m thoroughly enjoying your blog. I too am an aspiring blog writer but I’m still new to everything. Do you have any tips and hints for newbie blog writers? I’d definitely appreciate it.
Just wanted to say thanks for the information. The information was very clear and helpful, more so than many other resources that I have been trying to find on MDM. Thanks for sharing your knowledge!