Manage Chrome Firefox in Windows with Intune using WDAG(2/3)

In this article, we are going to discuss how to use Windows Defender Application Guard (WDAG) to manage Google Chrome and Mozilla Firefox in Windows from Intune using WDAG

My name Saurabh Sarkar and I am an Intune engineer in Microsoft. I have a YouTube channel and you can subscribe to the same to learn more about Microsoft Intune.
Background
We very often get requirement from customers wherein they wish to protect the data in the browser of their Windows 10 machines given that the same is used for accessing many enterprise application\resources.
Now from Intune we have the ability of managing IE and Edge for Windows via making use of the Windows Information Protection Policy (WIP). However conventionally the same cannot be leveraged out of the box for Chrome and Mozilla Firefox given that they are not enlightened applications (i.e. they are not MAM aware apps and cannot differentiate between corporate\personal data and comprehend the WIP policy)
Please refer to my below article which explains the difference b/w Enlightened and Un-enlightened application- https://techcommunity.microsoft.com/t5/intune-customer-success/support-tip-taking-a-look-at-wip-and-enlightened-vs/ba-p/499715
In this article I wanted to take a moment and discuss the various methods of managing Google Chrome and Mozilla Firefox via Intune in a Windows 10 device with emphasis on WDAG
Sidenote
- Even though we are transitioning to the new Chromium-based Edge, we still have customers making use of the Google Chrome\Firefox browser and wish to protect the corporate data within.
- As illustrated in the kb, the usage of OMA-URI\WDAG\Applocker XML is a workaround (if the customer chooses to protect the data in 3rd party browser) and it does not make the browser enlightened.
- This is not a recommendation to customers from a support perspective, it’s elucidative.
Overview:
As mentioned, given that Google Chrome and Firefox are not enlightened apps, they cannot be targeted via WIP policy. However, there are the below 3 possible ways of administering Chrome from Intune thereby protecting the enterprise data in the browser.
| S.No. | Approach | Applicability |
| 1 | Managing Chrome Browser via OMA-URIs using ‘Chrome – ADMX’ | Applicable for Chrome only |
| 2 | Making use of Windows Defender Application Guard (WDAG) | Applicable for Chrome, Firefox, IE and Edge |
| 3 | Using an Applocker xml for the browser | Applicable for Chrome and Firefox |
In this article, I wanted to take a moment and discuss the second option. The other 2 options have been explained in a different post
Use Windows Defender Application Guard (WDAG)
What is WDAG?
Windows Defender Application Guard (Application Guard) is designed to help prevent old and newly emerging attacks to help keep employees productive.
Application Guard helps to isolate enterprise-defined untrusted sites, protecting your company while your employees browse the Internet. As an enterprise administrator, you define what is among trusted web sites, cloud resources, and internal networks. Everything not on your list is considered untrusted.
If an employee goes to an untrusted site through either Microsoft Edge or Internet Explorer, Microsoft Edge opens the site in an isolated Hyper-V-enabled container, which is separate from the host operating system.
This container isolation means that if the untrusted site turns out to be malicious, the host PC is protected, and the attacker can’t get to your enterprise data. For example, this approach makes the isolated container anonymous, so an attacker can’t get to your employee’s enterprise credentials.
More details on WDAG- https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-defender-application-guard/wd-app-guard-overview
System requirements- https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-defender-application-guard/reqs-wd-app-guard
Use WDA using Intune for Google Chrome:
There are the following steps to this-
- Firstly, we will have to deploy a policy from Intune.
- Now we will have to install the Hyper-V and WDAG feature in the end device.
- Now we will have to get the Chrome browser ready (by installing an extension)
- Finally, we will have to install a supplementary application in the device- (Windows Defender Application Guard Companion app)
1-Policy Setup needed from the portal:
From the Intune portal we must make a Custom policy to govern the Windows Defender Application Guard and thereby using it to administer Chrome\Firefox.
For testing, herein we will define a couple of URLs which our organization trusts viz facebook.com and youtube.com. Apart for these websites all the other websites would be treated as untrusted.
How to setup WDAG policy
- Go to Device Configuration Profiles>Windows 10>Custom>Add.
- We will have to add 2 OMA-URIs here.
- In the first one would enable the Windows Defender application Guard
- In the second one, we would mention the URLs that we trust viz facebook.com and youtube.com.

#Once this policy is delivered to the device, we can see its status from the portal as succeeded.


2-Installing the Hyper-V and WDAG feature:
Go to control panel and select both the features as shown below-

At this point the Chrome browser behaves as normal and all the websites are accessible via the same.
- Preparing the Chrome Browser
#Click on the 3 dots (right top of the browser)>More tools>Extensions

#Now click on ‘Open Chrome Webstore’ as shown below:

#Now run a search for ‘Windows Defender Application Guard’ and click on “Add to Chrome”>Add Extension


#Once the extension has been installed, we would see a prompt as below

#Now when we open Chrome and try to access any website, we see the below message, stating that ‘Windows Defender Application Guard Companion app’ is missing.

- Installing a supplementary application in the device
- As seen above, we will now have to install an application called “Application Guard companion app” to make use of the browser.
- Now click on “Get it from Microsoft Store” in the above page.
- Now we will be redirected to the store and we can click on ‘Get’. This is a free app which can be downloaded without signing into the store as well


#Now we need to click on Install


#Once installed we will see a prompt as below and can see the app installed in the OS.


#Once the Companion app is installed, now if we open chrome, we see below–

Now the device and the Chrome browser are ready and protected. We can see the working behavior now as shown below-
Results–> Chrome
Now when we open Chrome and browser to ‘youtube.com’ (which is a trusted site as per our Intune policy) we see the below-


#And eventually the website will open up as below and it functions (normally as it would in any device).

#Now if we access any untrusted website like ‘google.com’.

#First, we see the below prompt

#Now the URL is redirected to an Application Guard Edge browser

#The URL now opens up in Edge as shown below

Now if we copy-paste any data from this browser to any other application, the same is prohibited.

Behavior in Firefox:
#By default, all the websites are accessible from Mozilla Firefox and we can copy paste data from any website in Firefox to any other app.

- To achieve similar behavior in Firefox as we saw in Chrome above, we will have to install the Application Guard extension in Firefox.
- We will click on the “Add-ons” option of the browser

- Now we will run a search for “Application Guard Extension” and click on the first search result (as shown below)


- We will now add this extension to Firefox.


Now the device and the Firefox browser is ready and protected. We can see the working behavior now as shown below.
Results – Firefox
Now if we open ‘youtube.com’(which is a trusted site as per our policy)- we are able to browse to it.
If we copy paste any data from Firefox (i.e. YouTube session) to Notepad, we can do the same.

- However, if we try to open any other website like ‘msn.com’ (not trusted as per the policy) we get the below message.

- The website’s session is redirected, and it now open up in Application guard IE

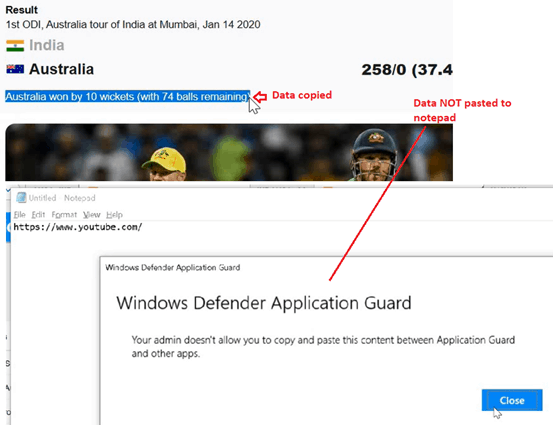
#Now if we try to copy any data from the browser and paste it to any other application, the same is prohibited as shown below.
Validation at Device
There are 3 locations wherein we can validate the same-
- Info>Sync
- MDM Diag Logs
- Registry



Net Result:
Using this approach, we can now as an admin-
- Set the websites (usually corporate\intranet based) that we trust.
- These websites when being accessed via Chrome\Firefox give the usual experience to the end user with no restrictions being imposed on the session.
3- We can now segregate the environment in which the browser session would run when it is being used to access any untrusted website.
4- The session of these untrusted websites are subjected to restrictions like- we cannot copy any data from the session to any other application in the device.
5- We are running the untrusted website sessions in a different virtual environment thus the device and the apps in the device are protected from potential threats originating from an untrusted website session.
6- We cannot customize the experience in the session completely using this approach, like setting bookmarks, etc. and the level of control at the browser is not very granular.
Conclusion:
There are multiple ways of managing Chrome and Firefox in a Windows 10 machine from Intune as illustrated above.
We can use either of them or a combination of them depending upon the use case and the level of restriction we wish to impose on the user’s browser session.
Resources
- https://cloud.google.com/docs/chrome-enterprise/policies/?policy=URLBlacklist https://www.chromium.org/administrators/url-blacklist-filter-format
- https://support.google.com/chrome/a/answer/7532419?hl=en
- Intune Application Deployment Guide Google Chrome Browser
